Mobile phones and Malwares(Viruses,Trojans,Worms etc: -)
MOBILE PHONE MALWARES.
Even though the first mobile phone malware was discovered in june 2004 which was the Cabir worm it was just a proof of concept written by the virus writing gang 29A and it was not dangerous as it was not set out in the wild. The came the variant of the Cabir, Mabir.A. Mabir was one step ahead in the social engineering technique. It acted more smartly by sending itself and MMS reply to the SMS or MMS received so that people and hence the recipient was more inclinded towards opening it.
The Commwarrior worm was the first malware to create a major havoc in the word of mobile phones. It operates on Symbian series 60 devices and being worm it is capable of spreading itself both over Bluetooth and MMS. In addition to spreadingitself over the network and also searches the users local address book for phone numbers and sends itself as an MMS to thecontacts. Unsuspecting mobile phone users open the MMS thinking it is from their contacts. This is the social engineering technique used here just like in case of most of the viruses, worms and Trojans in the PC world.
Some of the messages sent by Commwarrior to trick the user were "Nokia ringtonerNokia RingtoneManager for all models" "Audio drive Live3D driver with polyphonic virtual speakers!".
Read more info here.
Another Mobile phone Trojan that was first found in 2005 was the Fontal.A. It installs corrupted Font file into infected device, thus causing the device to fail at next reboot. However, there is only a small risk of infection and ones who arevulnerable to this are the people in the habit of installing warez mobile games files or some similar files onto their mobile phones.
Read more info here.
And for a while Java seemed to be the one that was safe from these kind of attacks. But just like I had noted in my article "Everything about Trojans and Anti-trojans", Trojans are finding a new home in the mobile phones through Java.
The first Trojan for J2ME (Java) was detected back in Feb 2006 and was called the Red Browser Trojan and it can run on a vast amount of mobile phones that supports Java.
The next one that has been making it's rounds is a Trojan associated with the Russian site games.gsmland.ru which sends SMS to a particular number (1717) and it sends 5 SMS at one time which costs $3 each.This one has been named the Trojan-SMS.J2ME.Wesber.a by Kaspersky labs.
SMS AND TROJANS
And another thing to be noted is that SMS is used by phone operators to make changes to the Mobile phones without user intervention. So what happens is that the phones do not check the source of the SMS to verify whether it is legitimate or not. So this loophole can be used by a malicious person. The possibility of this was demonstrated very recently by Wilfried Hafner of SecurStar. He demonstrated that by sending a bogus SMS he can not only change the settings of the phones but also eavesdrop on conversations and read the user's SMS. Hafner demonstrated this on Nokia E90 and a Qtek Windows Mobile 2005 phone by using an example Trojan called "Rexspy"
Flexispy is another software available in the market which is used for the same purpose and has the characterestics of "Rexspy" But this software has to be manually installed. So that means that even though it can't be remotely installed Flexispy can be easily installed into your mobile phones by anyone who has physical access to your mobile phone. Once installed it can be used to even remotely activate a mobile's camera or microphone.
Major mobile phone operators like Orange and Vodafone are viewing this threat seriously and are taken preventive measures.
PROTECTION

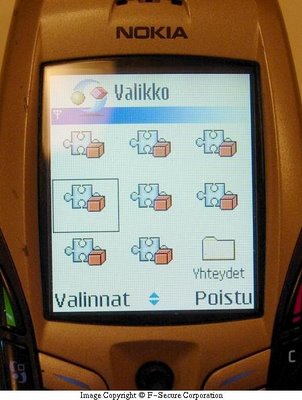
One of the best ways to protect or disinfect your mobile phone is to use the F-Secure's anti-virus tools for mobile phones. If your phone is WAP enabled and you can access the net directly from your phone you can directly go to the F-secure site and download it. If not the other option is to use your PC to download the software and then download it from your PC to your mobile phone. F-Secure offers a free 30 day trial version for each of the product. They offer this for a lot of mobile phones. You can download the trial version here.
Recently F-secure also added a firewall for smart phones. The firewall with ANtivirus is priced at $35 The product F-Secure Mobile Security can also be downloaded as a trial here. It supports symbian s60 and s80

The anti-Virus makers Trend Micro has recently released a new version of it's mobile phone security software which has a firewall. The software costs $35 which includes a years update and service. The ver 3.0 apart from the built in firewall has Anti-Spam for SMS Text Messages and Flexible Virus Scanning. Trend Micro offers a 30 day trial version. Currently the ver. 3.0 is available only for Windows Mobile 5.0 (PocketPC) and Windows Mobile 5.0 (Smartphone). Support for Symbian will be available soon. The ver.2.0 which does not have a firewall supports both Windows mobile and Symbian. You can download both here.
CONCLUSION.
The major reason for worry is that just like in the PC world the trend is to use if for espionage with the intention to blackmail or for financial gains. The trend has already started with the above mentioned commwarrior to Mabir.A that affects Symbian to the RedBrowser Trojan that affects using J2mE (Java) and the Flexispy software.
The mobile phone is a gadget that is always with you and it can carry the contact details and sensitive SMS and apart from the datas it carries if eavesdropped your conversation could give out a lot of sensitive information.
In the world of mobile phones smart phones are gonna be a major target. Symantec's stats show that while 80 per cent of companies allow corporate data on handheld devices, only 25 per cent have so far addressed smartphone security.
There haven't yet been a major outbreak of a mobile phone malware like that in the PC world except for the isolated outbreaks. But experts say that it is not too far. F-secure is already developing products that prevent the spreading of these malwares not only through the browsers etc but also through a wireless technology like Bluetooth. These kind of softwares could even help corporates to scan all the Bluetooth enabled phone in the premises for infection and thus alert them about someone having an infected phone in the premises.
SPECIAL MENTION : Bluetooth and Wi-Fi Hacking.
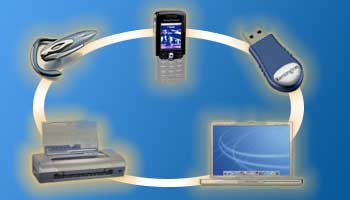
Apart from the world of the mobile phone malwares (Viruses, Trojans, worms etc:-) the world of Bluetooth hacking. This is an area we will cover later.One of the major problem with Bluetooth is that it is not easy to monitor like the normal Internet's network. The most common blue tooth exploits are Bluesnarfing, Bluebugging, Bluejacking and Denial of service. To have a better understanding of these terminologies take a look here.
But to completely exploit and eavesdrop using the Bluetooth the devices needs to be paired. And in 2005 it has been demonstrated by two Israeli students Yaniv Shaked and Avishai Wool that it is highly possible to pair blue tooth devices without even alerting the user. And they demonstrated that once a connection is set up the attacker could eavesdrop on data transmitted between the target devices and a PC or take control of someone's Bluetooth device. And once the two devices were paired the attacker could work out the link key in 0.06 seconds on a Pentium IV computer.
Also check out this page and on the left hand side you will see the 10 steps to protect your Bluetooth device.
Wireless hacking is another area and any mobile or laptops connected to a network through a wireless connection is very vulnerable to these attacks. If you check out this page you will be amazed to see the
number of tools available. However, these tools are made available by them only for educational and security purposes. They should not be used for any illegal activities.
And to get an idea about the wirless hacking techniques used and how to stay protected this computer world article even though published in 2004 is still worth having a look.
It is not surprising that apart from the Antivirus tools for mobile devices the Antivirus vendors are coming up with firewall and Intrusion detection softwares. Just like in the PC world it is advised to use a combination of firewall and Antivirus.
Other references:-
Techworld.
TheRegister.co.uk
Vnunet.
Related Reading:-
Everything about Trojans and AntiTrojans.

1 comments:
http://unwitting.multiply.com
Check out the link above. WORST CASE OF CYBERSTALKING I HAVE ENOUNTERED ever.
22 year old female from the Philippines. Poor girl.
Post a Comment